 When I was a high school kid, my dad and I sometimes played a game where one of us would make up a secret code, write a message in that code, and the other would try to decipher the message. We generally used simple substitution ciphers, so it was an exercise in letter frequency analysis and word guessing.
When I was a high school kid, my dad and I sometimes played a game where one of us would make up a secret code, write a message in that code, and the other would try to decipher the message. We generally used simple substitution ciphers, so it was an exercise in letter frequency analysis and word guessing.
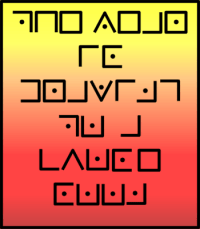
There’s a cute secret code I found in a book back then that really stuck with me because of the neat way it looks. It also stuck with me because it’s so simple that once you learn it, you really can’t forget it.
So, for some Saturday fun, I thought I’d share it with you.
The posts this past week were pretty technical, and there is more to come, so I thought a break over the weekend was called for. I’ll get back to the topic of computers and code next week. Today is about a completely different kind of code — secret code!
 And there’s really no connection with computers (secret codes long predate computers) other than that modern encryption is highly mathematical and requires computers to do effectively.
And there’s really no connection with computers (secret codes long predate computers) other than that modern encryption is highly mathematical and requires computers to do effectively.
I’d heard this code referred to as the “Prisoner’s Code” due to the ease of carrying the method around in your head.
As it turns out, it’s officially known as the Pigpen cipher and was used by the Freemasons so much it’s also known as the Freemason’s Cipher.
It is a straight up mono-substitution cipher, so cracking it is trivial once you get past the unusual way it looks (essentially, with such ciphers, you’re just playing a game of Wheel of Fortune).
Incidentally, the way this cipher looks makes it pretty strictly a hand-written one. Even Unicode doesn’t have these glyphs! (At least not so far.)

A Pigpen Cipher
We start by writing out the alphabet in the pattern shown to the right. The first nine letters (A-I) in a “tick-tack-toe” grid and the next four (J-M) clockwise around the big X.
We repeat that for the next nine (N-V) and four (W-Z).
To write a message in this code, just use the shape that surrounds the letter. For example, ‘E’ is fully surrounded by four lines, so the code for an ‘E’ is a box.
If the letter comes from the lower set (N-Z), put a dot in the center of the shape. (So, the code for “R” is a box with a dot inside.)
That’s all there is to it. You should be able to crack the code shown at the top of the post now. Here’s another sample you can practice on:
“Vanna, I’d like to buy an ‘O’, please…”
Cracking a code like this is pretty easy, especially when words are left intact. As I mentioned, it’s basically a game of Wheel of Fortune (but no buying a vowel, although in the game my dad and I played, if you got stuck, you could ask for a hint).
If you see a one-letter word, that code almost has to be an ‘A’ or an ‘I’ — you can look elsewhere in the message to see where it’s used again. A two-letter word can be ‘AS’ or ‘TO’ or ‘IT’ or some others, but you already have ‘A’ being used twice. Even three-letter words can be helpful clues (‘THE’ is very common).
Typically, if we’re serious, one of the first things we do with secret codes is mush all the words together and then break them into, for example, five-letter groups (with padding to fill out any short last group). It requires a little thought reading such a message, butyo ucanu suall yfigu reito utwit halit tleef fortx.
§

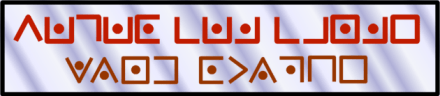
“Alienese”
If you watched the great TV show Futurama, you often saw samples of a written “alien language” using weird symbols.
That alien text — Alienese — was coded using a substitution cipher created by the show’s writers. For those willing to spend time decoding the language, there were often additional jokes.
The writers of The Simpsons and Futurama have some strong attachments to mathematics, and both shows are peppered with interesting math references for fans with some math background!
Something that, in general, is astonishing about both shows is how much is put into each episode that you never really see unless you can stop and view it in slow motion. Sometimes you even need to go frame by frame to pick up some little Easter Egg.
 More and more, clever creators of clever modern TV shows include things that require freeze-frame or slow-motion to appreciate.
More and more, clever creators of clever modern TV shows include things that require freeze-frame or slow-motion to appreciate.
Some of that is for their own amusement with no expectation of viewers seeing it, but increasingly there is an expectation some viewers will closely examine any document or interesting background bit.
Which may come, in part, from such viewers spotting some really funny, let’s call them, mistakes and then mocking the show or film for it. Visual storytellers today know that some viewers will examine the details closely!
For example, some like to freeze-frame and actually read any newspaper closeup. Often the text is gibberish, or one paragraph repeated over and over. The expectation is that viewers normally only have time to read the headlines.
Sometimes the text is grabbed randomly from a real newspaper, and the headlines are hilariously mismatched with that text. Or the story they wrote for the headline is repeated under other headlines.
§
Decoder rings work in similar fashion to the codes discussed so far, although most of them map the alphabet onto a shifted version of the same alphabet (rather than weird made-up symbols).
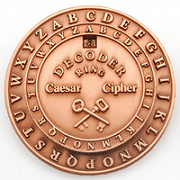 The shift means that, if ‘A’ maps to, say, ‘G’, then ‘B’ maps to ‘H’, ‘C’ maps to ‘I’, and so on. ‘Z’ wraps around to ‘A’ so here ‘U’ maps to ‘A’ and ‘Z’ maps to ‘G’.
The shift means that, if ‘A’ maps to, say, ‘G’, then ‘B’ maps to ‘H’, ‘C’ maps to ‘I’, and so on. ‘Z’ wraps around to ‘A’ so here ‘U’ maps to ‘A’ and ‘Z’ maps to ‘G’.
Knowing the shift, just what ‘A’ maps to, tells you the entire pattern.
A slightly more sophisticated version maps each letter to a scrambled version of the alphabet. Knowing one, doesn’t help with the others (except in eliminating possibilities).
There’s a version of the straight shift called ROT-13. It was used on the internet for many years to shield innocent eyes from dirty jokes and movie spoilers. There was nothing particularly secret about it, it just made text unreadable unless you decoded it.
ROT-13 (rotate 13) used the fact that the alphabet is 26 characters. More to the point, it used the fact that number divides in two evenly. All the code does is map the first 13 characters (‘A’-‘M’) to the second 13 (‘N’-‘Z’) and vice versa (so an ‘A’ becomes an ‘N’ and an ‘N’ becomes an ‘A’).

Set decoder to ROT-13!
Unlike the Pigpen or Futurama codes, ROT-13 does handle upper- and lower-case letters. That 13-character double-shift is applied to both cases. You can even do a “ROT-5” on any digits (mapping ‘0’ to ‘5’ and vice versa).
Decoder rings handle both text cases implicitly (ROT-13 is just a setting on most decoder rings, ‘A’ is mapped to ‘N’).
Of course, that means both cases have the same mapping (‘A’ and ‘a’ are, for example, ‘N’ and ‘n’ respectively).
As secret codes go, it isn’t very.
§
Merely scrambling the mapping doesn’t actually improve anything.
So long as the same letter always maps to the same code, the message is trivially easy to break. It remains a game of Wheel (which, especially with decoder rings, is appropriate).
The code becomes much better if you change the mapping for every character. The first letter uses one scrambled version, the second letter uses another, and so on. (The infamous German WWII Enigma code machine did exactly this. Its fatal flaw was that a letter never mapped to itself.)
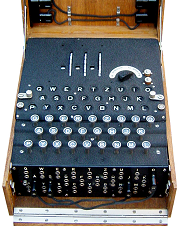
Enigma code machine.
Generally, there is a limited number of mappings, so if the message has more characters than mappings (which is the usual case), characters use the available mappings repeatedly in order.
That, unfortunately, makes the code possible to crack.
Not by you or me, perhaps, but by experts. There are sophisticated mathematical tools that can crack just about any substitution code.
Here, an interesting characteristic of language is its redundancy and verbosity. While those facilitate human communication, they make substitution ciphers vulnerable to analysis.
§
There is a substitution code that is uncrackable (if you don’t screw up). It’s called a One Time Pad (OTP). Essentially, it requires a secret pattern of changing the character mapping that’s as long as the message.
Typically, you generate a random key the same length as the message and then combine (for example, with an XOR operation) each character in the key with the corresponding character in the message to generate a new code character.
The vulnerability here is the key vulnerability of all secrets: the human factor. An OTP requires keeping the key secret (plus you need to know how to generate truly random keys). Worse, it requires safely transporting the secret key to those who need to decipher your message.
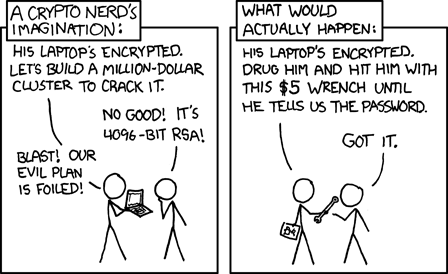
As usual, xkcd has a comic that says it all.
If you can safely transport a secret key (as long as a message!), then why can’t you safely transport a secret message the same way?
One answer is that you can generate an extremely long keypad — long enough for many messages. You risk transporting the key, but much less often than messages.
Still, there is that risk, plus the risk of the key being found by the Wrong People. (You’ve seen in movies the trick of using a book as an OTP. Messages are strings of numbers that refer to words in the book. There is nothing suspicious about a book, especially if you have a number of them.)

Turing’s Bombe machine.
Modern encryption takes a whole other approach that involves public keys shared with the world and a private key you don’t share.
Others use your public key to create coded messages for you that only you can decode (using your private key).
The processes are very mathematical and abstract, but one thing that’s interesting here is how areas of mathematics thought previously to have no possible use — seemingly obvious mathematical toys — have turned out to be instrumental in modern encryption.
And, once again, it’s a place in life where some sophisticated math is going on. Anytime you go to an https website (rather than plain old http), you’re using modern encryption (the ‘s’ stands for secure).
You just can’t get away from the stuff!
∇












October 24th, 2015 at 4:48 pm
Curious about the paper Lila is holding, but don’t want to bother trying to decode it? It says: ARRQ RKGEN PNFU? ZRYG QBJA LBHE BYQ, HAJNAGRQ UHZNAF, JR CNL GBC QBYYNE!
In ROT-13.
And if you just can’t handle the whole decoding thing at all, it says: NEED EXTRA CASH? MELT DOWN YOUR OLD, UNWANTED HUMANS, WE PAY TOP DOLLAR! (Highlight the text in the box to reveal it.)
June 12th, 2022 at 4:20 pm
[…] and complex, for encoding messages has been a minor fascination. (I posted about those early days back in 2015 and more recently about other codes from books. See The Playfair Cipher and Secret Code II. And […]
September 5th, 2023 at 6:12 pm
[…] Secret Code (Oct. 2015; 58) #38 overall. A post about (simple) secret codes with a little about the German Enigma machine. […]
September 9th, 2023 at 3:11 pm
[…] written about secret codes before. The Pigpen cipher was pretty simplistic, almost more a child’s game, but the Playfair cipher was a bit more […]
March 29th, 2024 at 6:51 pm
[…] amateur detective Lord Peter Wimsey (by Dorothy L. Sayers). While I’ve always enjoyed secret codes, I’d never heard of the cipher Sayers used — the Playfair […]
July 4th, 2024 at 6:09 pm
[…] Secret Code (140) […]